We develop and support digital healthcare solutions for pharma, medtech and life science – regulatory compliant, patient-centered and technologically leading. Our portfolio includes medical software, DiGA, DTx, companion apps, digital biomarkers, DHT, medical apps, secure connectivity, cloud solutions, AI, cybersecurity and ISMS. Whether MDR, FDA or BSI-compliant: together we are shaping the digital healthcare of tomorrow.
Behind every success story are strong partners. Here you will find a selection of our customers who have worked with us to implement innovative solutions and achieve their goals. This collaboration is proof of our commitment and expertise – and motivates us to continue to deliver top performance in the future.









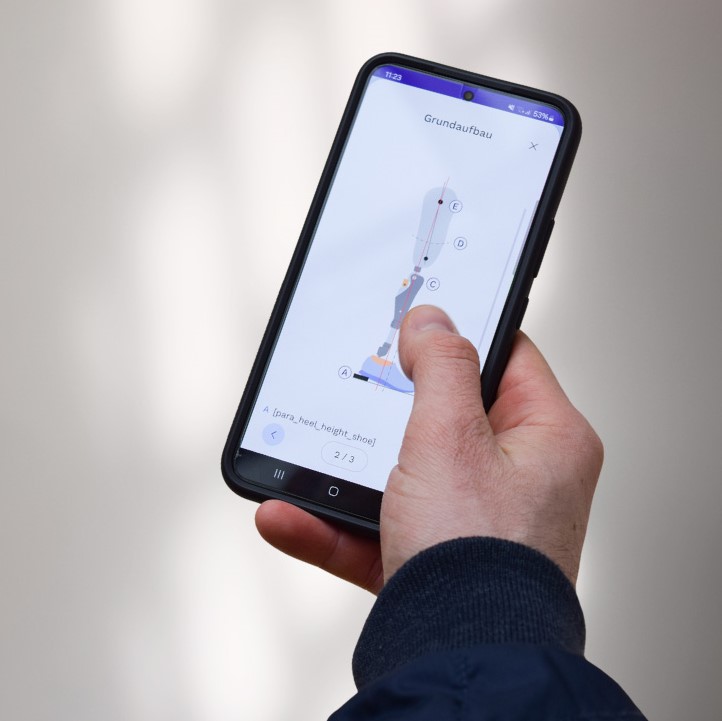
Mobile medical and healthcare apps enable users to act independently and provide doctors with a data-based diagnosis. Our portfolio includes apps and digital health applications (DiGA), for example in the areas of diabetes or women’s health, as well as health economic business solutions.
Numerous medical professionals and doctors count on the support of our medical products. With our healthcare platform MedicalOne Connect DTx, we are revolutionizing collaboration in the healthcare sector by seamlessly connecting medical technologies, healthcare professionals and patients – GDPR-compliant, secure and cost-efficient.

Mobile medical and healthcare apps enable users to act independently and provide doctors with a data-based diagnosis. Our portfolio includes apps and digital health applications (DiGA), for example in the areas of diabetes or women’s health, as well as health economic business solutions.
Numerous medical professionals and doctors count on the support of our medical products. With our healthcare platform MedicalOne Connect DTx, we are revolutionizing collaboration in the healthcare sector by seamlessly connecting medical technologies, healthcare professionals and patients – GDPR-compliant, secure and cost-efficient.